The uses of Wifi Auditor

Date: 2014-05-20 07:18:30
By:

Wifi Auditor is a tool that analyzes nearby wireless connections, identifies the make and model of the router and provides you with the factory default WPA-PSK password for them. Of course, by now you’re thinking this is rather dodgy and suspicious, but don’t be alarmed. Wifi Auditor is a tremendous tool in protecting both private personal networks as well as corporate ones.
Let’s say you have your home network and you have set up the WPA security but didn’t bother setting a password for it and left the factory default. Don’t feel guilty, as it’s actually pretty common. We like to trust that the password provided is good enough. Well, with the auditor you’ll know if that password is indeed as secure as you think; and if not, well then you know you need to change it.
While Wifi Auditor is pretty powerful, it doesn’t work with all routers. If you are worried about someone breaking into your network and don’t completely trust that changing your password would protect you from someone unscrupulously using the software against you, then you can use the list of models and makes to determine which routers NOT to get in order to protect yourself. In fact, once acquired, you can use Wifi Auditor to confirm that you are indeed safe.
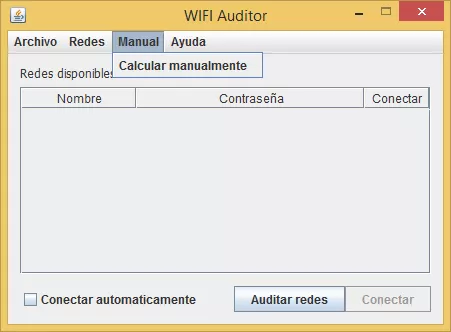
If you have multiple networks, something very likely to happen in a corporate environment, then the software will help you maintain security at the press of a button. When you first launch the application, it lists all available networks. Pressing the Audit Networks button will analyze each of the networks for vulnerabilities, clearing the list of available ones if it doesn’t find any. This can be a tremendous help to you, the network administrator, because you won’t need to check all routers for security reasons, unless a few of them aren’t on the list mentioned in the previous point.
If by any chance the auditor does find vulnerabilities and can connect to the network, it will give you a full report on your connection, identifying all security issues. Carefully reading this report will not only help you reinforce your network but it will also tell you if you have intruders hijacking your bandwidth, which depending on whether it’s a personal or a corporate network could mean very bad things.
If you have any doubts about your network’s security, then download Wifi Auditor today and use it to protect yourself.
Give Away: Get a Driver Booster license key for FREE!
Driver Booster is an essential program to keep all your drivers up to date, it is a must have for anyone that wants to keep their computer updated with all the latest drivers the moment that they are released. It has been so popular, it is our most downloaded program in our System tools ...
Bytes that Rock Winners announced: Discover the best games, programs and blogs of 2015!
As you may be aware we recently held the Bytes that Rock Software Awards recognizing the best software, games and blogs from the last twelve months for their hard work and the fantastic programs and blogs they have given to us during the last year. We are pleased to say it was hugely successful, thanks to ...
WHAT TO EXPECT from WINDOWS 10 OS: Release date, Cost and New Features
BASIC ANSWERS TO BASIC QUESTIONS - What? Windows 10 is a complete upgrade from all the previous Windows operating systems. - When? Summer 2015, the exact release date has yet to be confirmed. - What’s the cost? Will it be free? Windows 7 and 8.1 users will enjoy a free Windows 10 ...